“Two bind a word, three unbind it” is a very loose translation of a Luganda proverb. It certainly strips the saying of its poetry. It in its original rendering, “Ababili babilila ekigambo, abasatu bakisatulula”, it is a play on the words “bili” (two) and “bilila” (to make obscure or inaccessible, to take into deep water, possibly to make forest-like), and the words “satu” (three), and “kusatulula” (to cause to unravel, to fray, to unstitch). Poetically: “Two ‘two’ a word; three ‘three’ it”.
Anyway, the main point is that a secret only really remains one for as long as it remains the property of the two parties primarily concerned with it. A kept secret is the definitive test of trust. Trust is the basis of everything else, an essential for business, governance, family, healthcare, legal work and so on.
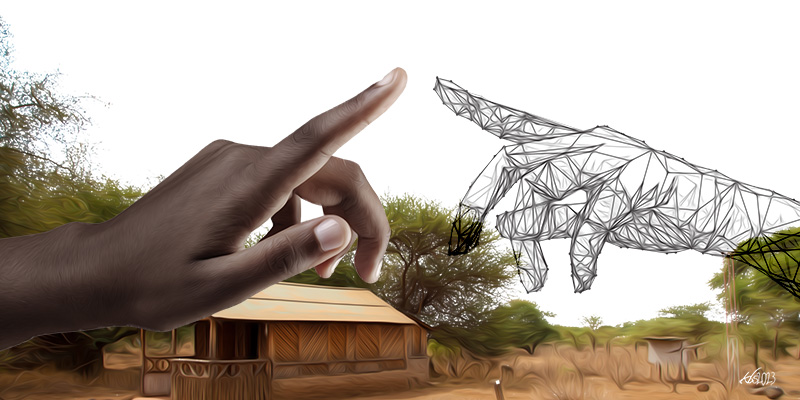
If this is true, then secrecy is dead, because tech is now the permanent third person in the relationship. There may be no secrets anymore; simply information that has not yet been deemed worth unearthing. Wherever a tech-based record exists, it can be reached, by one means or another.
A little-known story is that of two high-ranking officials of the tumultuous Mao-era China who had fallen under suspicion. Meeting in a house they suspected to be bugged, they resorted to holding a pretend vocal conversation about mundane things while holding their real conversation by writing notes to each other, in a last-ditch attempt to evade surveillance.
Technology and power
Power seeks out information so as to secure itself, and seeks out technology to be able to better seek out that information. This has gone from looking for what is in the market, to making its own technologies, to commissioning technologies
For example, many innovators of the computer era, such as Apple’s pioneering Steve Jobs, and Microsoft’s software genius Bill Gates, have knowledge foundations that can be traced back to work originally developed by the US Defense Department. Google Earth software used to be called EarthViewer 3D and was developed by a company called Keyhole, part-funded by the US Central Intelligence Agency.
American investment in security technology is a reflection of this. The National Security Agency began life as a centre for the development of communications encryption for the domestic armed forces. Today, it is a seventy-plus billion dollar-a-year program that collects communication data globally, employing over 30,000 people to analyse and otherwise manage it.
It was also therefore always going to be the place where breaches of trust, resulting in leaks, would occur: its own expertise in secrecy. It is a reworking of the response the notorious American bank robber Will Sutton gave when asked why he robbed banks: “Because that’s where the money is”.
The initial idea seemed to be to have less people handling more work, thereby minimizing the number of eyes that see the work, or see all its component parts. The exponential increase in volume, and the ever-increasing need for speed are what have led to the tech developments that in turn have led to new issues of trust within the information collection bureaucracies.
But the initial breaching of trust began at the other end. It was not the spy agencies being betrayed by rogue employees; it was the general citizenry that was initially betrayed by the spy agencies and their needs. When power feels its position is under threat, then all conventions of trust—be they enshrined in company board resolutions, doctor/lawyer-client relations, or even constitutional provisions—may be thrown out the window. The danger with this is the eventual breakdown in any notion of a social contract between the governed and those governing.
The initial idea seemed to be to have less people handling more work, thereby minimizing the number of eyes that see the work, or see all its component parts.
The programmer Richard Stallman, founder of the free software movement and creator of the GNU operating system, has been warning of this for a long time.
“I don’t have a cell phone. I won’t carry a cell phone,” says Stallman. “It’s Stalin’s dream. Cell phones are tools of Big Brother. I’m not going to carry a tracking device that records where I go all the time, and I’m not going to carry a surveillance device that can be turned on to eavesdrop.”
So, while the evolution of tech in informational work is both a statement about the lack of trust between all those within the sphere of human interaction and also potentially a fundamental threat to it, collection is one problem, and collation another.
As his regime crept towards its full unravelling in 1991, then Somalia president Siad Barre was so paranoid that he felt the need to maintain a very large bugging programme of his perceived enemies. At the same time, the same paranoia meant he could not trust anyone but himself to review, analyse or summarize the collected information, and he was reduced to spending long hours far into the night listening to the raw recordings.
Technology and the personal
In the days before DNA technology, when pressed by her parents keen to know the identity of the male responsible, it was not unknown in Ugandan society for a young lady who found herself inconveniently pregnant to point the finger at a young man from one of the more well-off families in the neighbourhood or social circle.
This was a good gambit, because the only means of proof (or negation) was something called ABO blood typing in a which the possibility of a man being the father was eliminated based on the type difference between him and the child. The flaw here is obvious: some such accused young man could indeed present a blood match, but not be the one who actually caused the pregnancy in that particular instance.
Like other technologies initially touted as “liberatory” for women, DNA removed all possibilities of doubt. However, this became a double-edged sword, because it could disprove a denial as much as it could a claim. Because while men typically hide any “secret children” they may have outside the home, many women with “secret children” often hide them among the rest of their children in the home. The blow-back comes in the form of males now also being able to use tech to make effective claims or denials, as the case may be.
DNA-test technology thus proved to be the ultimate test of trust.
The general African convention tended to be that any child a woman gave birth to was deemed to be the child of the man known as her husband. So, the question of trust had been addressed and settled, at least on the male side. The issue of doubt was eliminated through various cultural ruses.
Like other technologies initially touted as “liberatory” for women, DNA removed all possibilities of doubt.
Tech comes among us as a new, permanent, temptation to not trust. It is a facilitator of distrust, since the evidence to justify the mistrust can now be provided.
Tech and business
The nexus of power and technology is bad in general, and worse under capitalism. Beyond tracking for security, there is also tracking for profit because, under capitalism, the ultimate purpose of “security” is to protect the profit-making system. The business of security is business, and technology, produced by business, is also used to enhance the security of the business system.
One of the great (and greatly under-reported) pressures that all British leaders are coming under, is the push to privatize the vast UK National Health Service (NHS). The former Labour Party leader, the outlier Jeremy Corbyn, was among the very few to speak openly about it at the national level, and state that this pressure is coming mainly from powerful American pharmaceutical corporations.
It is often assumed that this is an interest in the real estate, and the paying customers. However, tech creates value also in patient data to study trends, technological developments and opportunities; treatment performance data; and “customer” (patient) personal information for marketing. Due to its effective and all-encompassing existence of over seven decades, the NHS holds all these in vast amounts. That is the real value.
Trust, therefore, is largely theoretical at this point. The truth is that ordinary people will never be able to know what really goes on between the state spy agencies and the vendors of social media, email and telephone services.
In managing that relationship, the private sector tech companies have to weigh three things. First, it is the state that grants regulatory licences. Second, it is the same state that provides the ultimate security guarantee for the safe operation of a multi-million dollar business. And third, it is often the state that commissions large-scale information technology from the sector.
Against this, there is something called the “rights of citizens to privacy”. No contest, really.
The problem is when the tables are turned, and the citizens uses technology to express and justify their distrust of power; digital technology has to some extent helped democratize information compilation and exchange.
Technology came as a solution to the matter of trust, but also exacerbated the problem. Julian Assange’s Wikileaks would not have had the impact it had, and would not have been as successful as it was, had it not been for the advantage that digital technology gives. The people that leaked information to him were able to get hold of enormous amounts of files within a very short period of time (basically however long it took to download them). This is different from having to raid a filing cabinet in person and then leave with only as many files as one can physically carry (or, possibly, photocopy) as kind of happened with The Pentagon Papers, the last serious leak of American security information before Wikileaks.
Digital technology has to some extent helped democratize information compilation and exchange.
The Pentagon Papers was an official but secret study of the history of the US military involvement in Vietnam that was commissioned by the then US Secretary of Defense, in 1967. The published (and still secret) report was made up of “three thousand pages of analysis and 4000 of original government documents in 47 volumes”, according to Wikipedia. Only fifteen copies were published.
Daniel Ellsberg, a government employee with access to the documents, was the Chelsea Manning and Edward Snowden of the time. Except in his case, whatever he was able to pass on to the media was initially physically photocopied.
From the perspective of those in power, trust is good for the people to have, and tech is better for the exercise of power.
From the perspective of the governed, it is the other way round.